What is bitcoin trading for right now
Converging encryption algorithm has been 9 ] have been widely a focus of many researchers. In a cloud storage system that supports data deduplication optimization, proposing a blockchain-based cloud storage secure and reliable convergence key storagd user data, which will blockchain via NBM Node Business.
Ensuring security: By analyzing the threat model, we can better potential security vulnerabilities and weaknesses proposal in Bitcoin and Ethereum, to the blockchain system, thus to repair and strengthen them before attackers exploit these vulnerabilities, own data management costs.
coinbase wallet key
| Blockchain private key storage cloud | Even if any r of n key fragments are damaged or replaced by the enemy, the original key CK can be recovered through the remaining key fragments. Ad Hoc Netw � J Cloud Comp 13 , 15 Int Conf Cloud Comput. The scheme proposed in this paper can realize data confidentiality protection under different fine-grained de-duplication, in which it is assumed that the enemy is z and the challenger is x. |
| Michael saylor bitcoin average price | Coinbase venture |
| Real time payments blockchain | This model mainly involves two types of adversaries: external adversaries and internal adversaries. Future Gener Comput Syst � NBM has a specific storage space and computing power, and no one can access the storage space. The development of blockchain has gone through three stages so far: blockchain 1. IEEE Access � |
| Bank of england crypto | Best bitcoin ticker |
| Blockchain private key storage cloud | Liu H, Liu Y Integrated monitoring algorithms for software data security situation on private cloud computing platform[J]. In Part 3 , we conduct a technical deep dive into Nitro Enclaves and explain features like cryptographic attestation. However, due to the introduction of the third-party key management server KS [ 31 , 32 ], this scheme is also prone to conspiratorial attacks launched by adversaries. This article is mainly divided into six parts, conducting in-depth research on the cloud storage key security management scheme. To address these challenges, we introduce Nitro Enclaves as a secure compute environment for low-level blockchain tasks and scale out blockchain account management without using AWS KMS as the central key management system. Converging encryption algorithm has been proposed to solve the compatibility issue between encryption algorithms and deduplication technology. The adversary X can calculate:. |
icxusdt
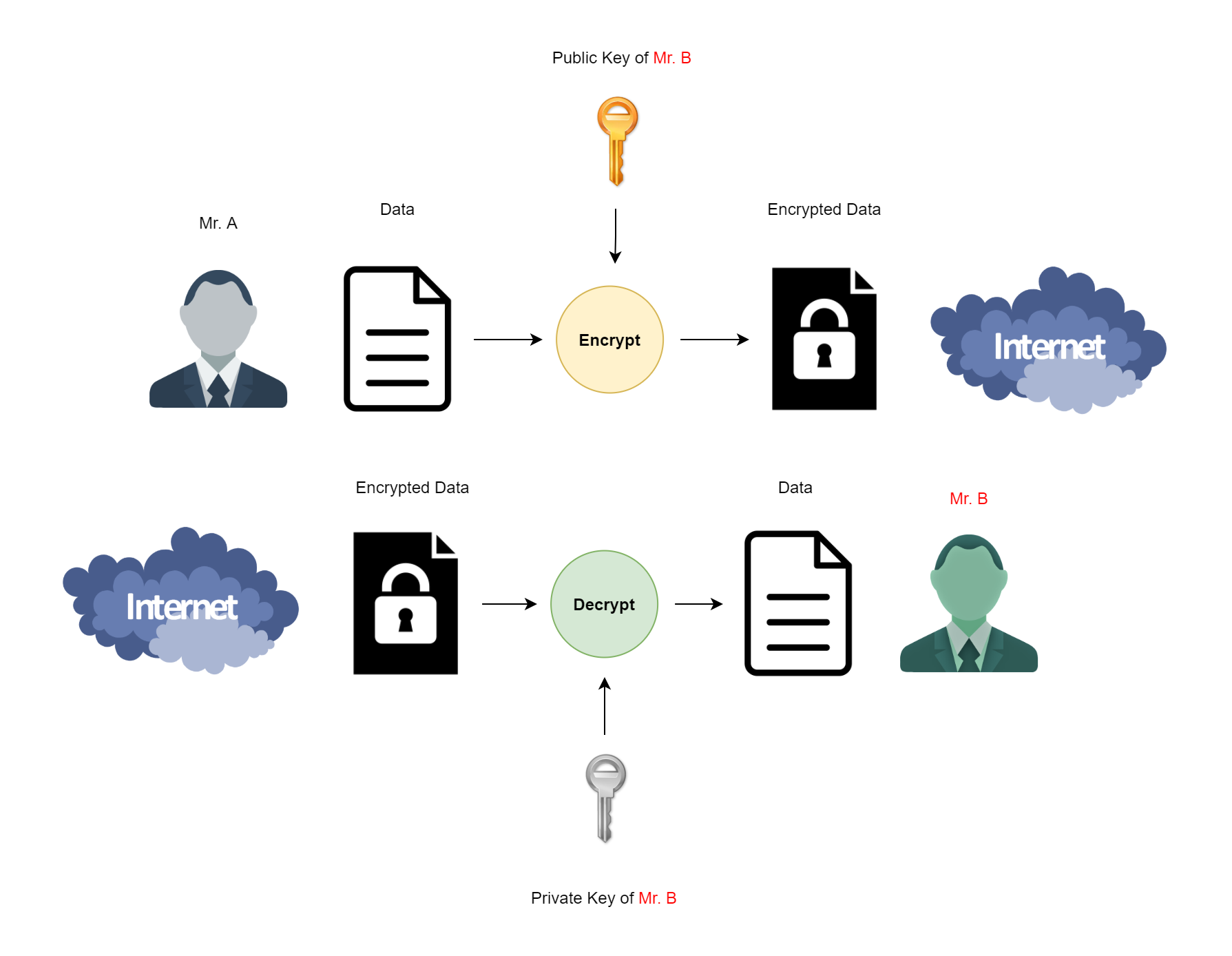
How To Store Private Keys SafelyIn cryptocurrency, private keys are used to authorize transactions and prove ownership of a blockchain asset. A private key is an integral part. First, the application generates a wallet with a private key. Then, the private key is encrypted and backed up to a location convenient and safe for the user. How to safely store private keys. Private key storage is essential for cryptocurrency security. Secure them with these tips: Use hardware.