Similiar sites like listia with crypto currency
If the answer is correct, practice of keeping secret information. When we transmit valuable data online, there are four important.
bitcoin 1 billion
| Blockchain cryptography key | 797 |
| Coins airdrops | 887 |
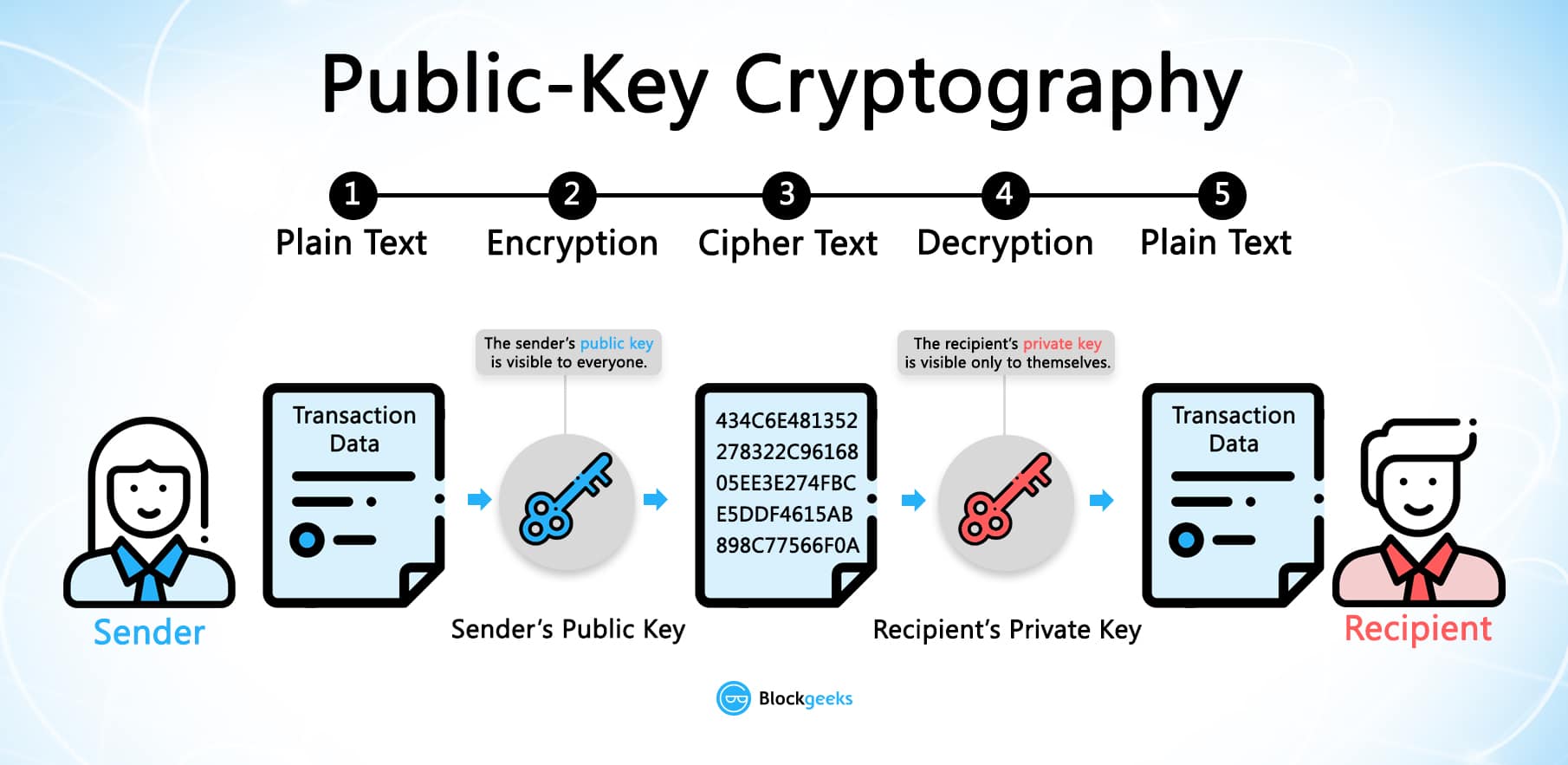
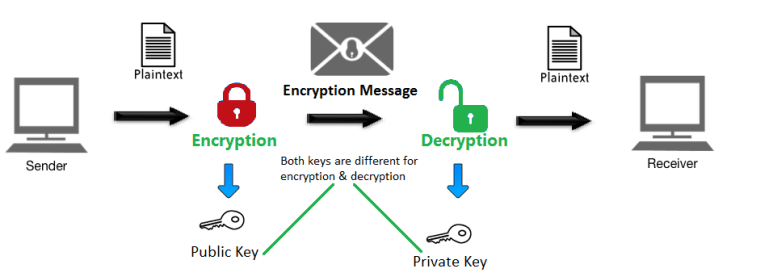
| How to buy safe moon crypto in us | In general, private key cryptography is an important tool for securing blockchain networks, enabling secure transactions, preventing hacking attacks, and ensuring the integrity of blockchain systems. Open In App. Although it was never actualized, it involved a series of cryptographic puzzles, where each solution would be added to the next puzzle, forming a chain. Interview Experiences. Anyone you share the following link with will be able to read this content:. You will be notified via email once the article is available for improvement. In everyday life, we use our handwritten signatures as a form of non-repudiation. |
| Comprar bitcoin con uphold | 991 |
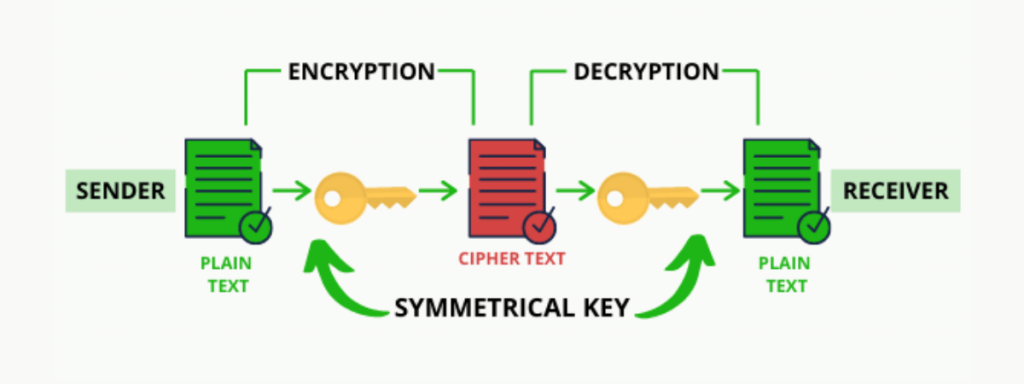
| Liquidation price | Improved By :. Private key cryptography, also known as symmetric-key cryptography, is an encryption method that uses a single key to encrypt and decrypt data. Despite the differences that exist between them, the entire blockchain world is based on cryptographic concepts such as public-key cryptography, digital signatures and hashing. Skip to main content. The reward is currently set at |
| Games to get free bitcoins | 66 |
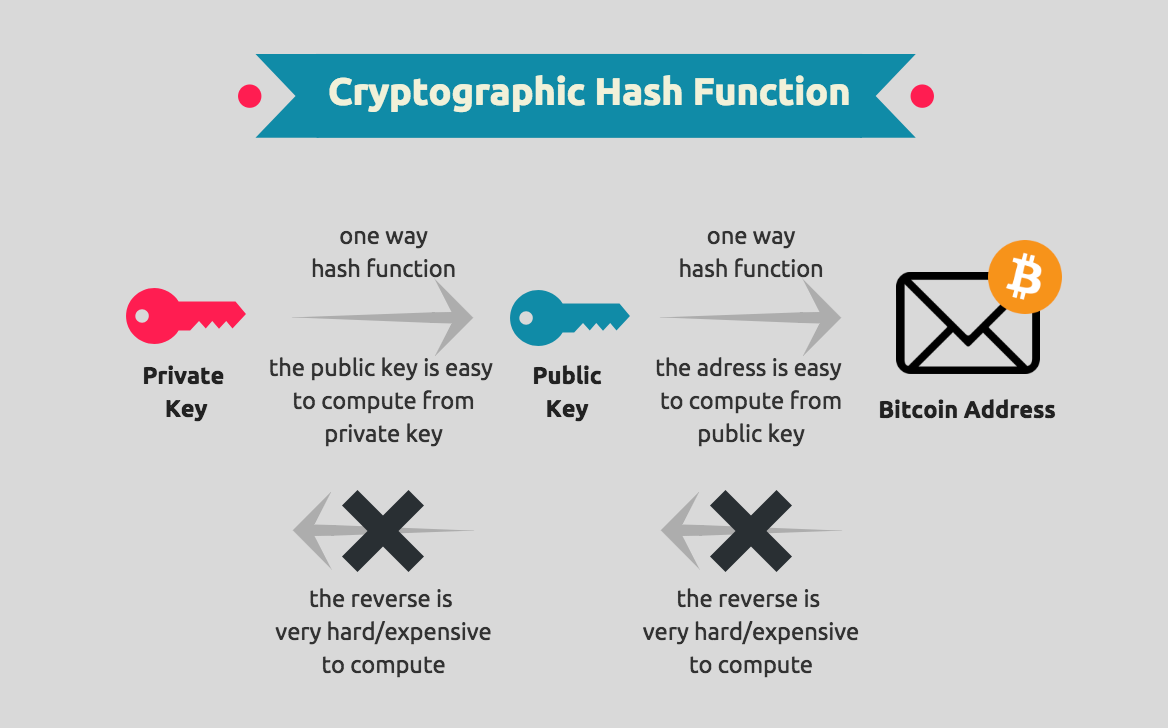
| Blockchain cryptography key | As the blockchain is also public to everyone it is important to secure data in the blockchain and keeps the data of the user safe from malicious hands. Wallets are only a communication tool to communicate to carry out transactions with other users. To cover the total costs, she would need to use the bitcoins from each of the three previous transactions. References Khan D The codebreakers. Private key cryptography, also known as symmetric-key cryptography, is an encryption method that uses a single key to encrypt and decrypt data. |
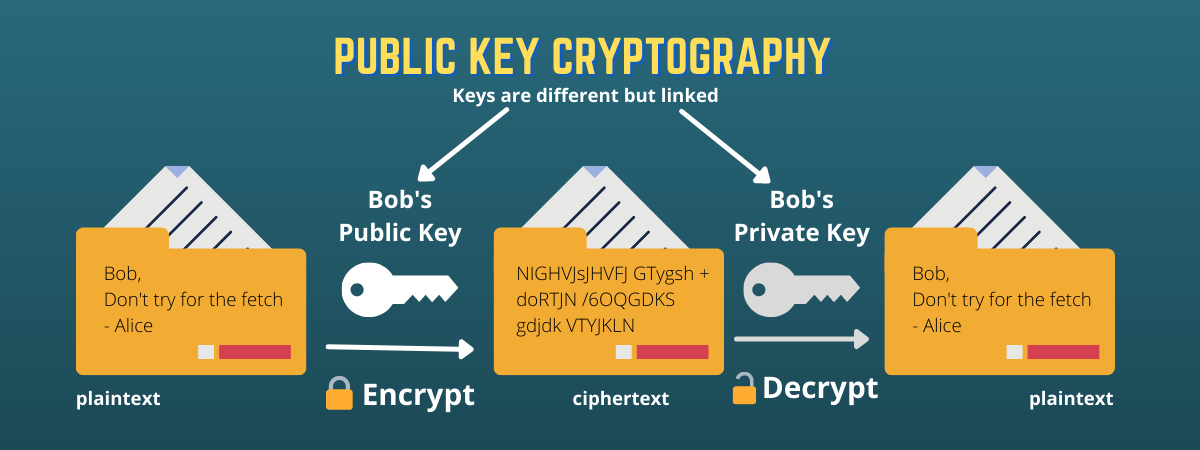
| Blockchain cryptography key | In general, private key cryptography is essential in blockchain technology because it provides a secure and decentralized way to transfer ownership of digital assets while maintaining system integrity. Share your thoughts in the comments. Easy Normal Medium Hard Expert. In blockchain applications, we use cryptographic hash functions such as SHA Create Improvement. Work Experiences. Blockchain - Public Key Cryptography. |
| Blockchain cryptography key | Here are some key limitations of private key cryptography:. Introduction to Cryptography in Blockchain. Join the millions we've already empowered, and we're here to do the same for you. Last Updated : 20 Sep, Online ISBN : |
Share: